|
|
2/29/2012
RunAuto Trojan
02/29/12 - This malware is a trojan downloader. RunAuto Trojan connects to multiple online
resources and downloads
various programs from there. There may be several parasites among
the downloaded software, that's why it's always a good
decision to get rid of RunAuto Trojan as
soon as possible. Please use one of the automatic removal tools listed below
to eradicate this
parasite.
RunAuto Trojan properties:
• Changes browser settings
• Connects itself to the internet
• Hides from the user
• Stays resident in background
     
3:11 pm est
2/28/2012
Win32.Zafi.b 02/28/12
- Win32.Zafi.b is the name of a threat that you may see in a faked security alert
message. This message mainly appears
with Perfect Defender 2009; a rogue application,
infection. This
program intimidates by showing fake security alerts to users in an attempt to
force them into purchasing
this fake program. Win32.Zafi.b worm spreads via infected video
codec's and file sharing networks. The bad side of this
“goodie” is the ability to disable antivirus
and other security products on a user’s computer (increasing
the potential for infection). To
avoid problems that Win32.Zafi.b can bring we highly recommend you to use reliable
anti-
spyware. Please use one of the automatic removal suites below to eradicate this parasite.
Win32
Zafi b properties:
• Changes browser settings
• Shows commercial adverts
• Connects
itself to the internet
• Hides from the user
• Stays resident in background
     
9:10 am est
System Check
7:09 am est
Uplink
02/28/12 - Uplink is an adware program that installs an Internet Explorer add-on, which replaces banners and ads
in web sites visited with its own commercial advertisements. The threat also gathers some network information and transfers
it to a predetermined web site. Uplink runs every time the user launches the web browser. Uplink
properties: • Shows commercial adverts
     
7:04 am est
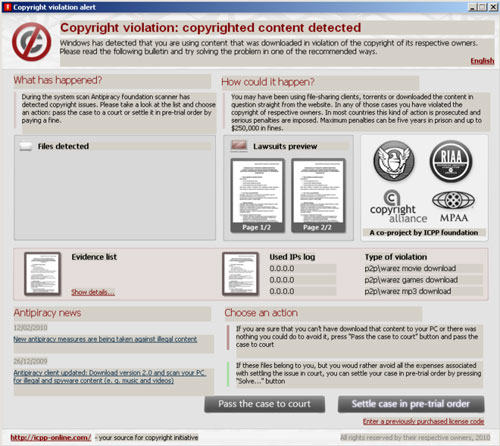
Copyright Violation Alert 02/28/12 - Copyright violation alert titled 'fake I-Q Manager Antipiracy foundation scanner' is the
latest ransomware
that prompts users of compromised systems to pay a fee for copyrighted
materials such as songs, movies or software.
Once installed, it will scan your computer for files
with .torrent extension and then will state that copyrighted material
has been found on your PC
and that you should pay a settlement of $399.85 or pass your case to the courts. Of course,
you shouldn't pay any fee and you shouldn't give them your credit card information for any reason.
This is nothing
more than a scam. Instead, please use a legitimate security suite (listed below)
to remove Copyright violation
alert ransomware from your computer as soon as possible.
This ransomware variant has been localized to the following
languages: Czech, Danish, Dutch,
English, French, German, Italian, Portuguese, Slovak and Spanish. Here's how it reads
in English:
Copyright violation alert
Copyright violation: copyrighted content detected
Windows
has detected that you are using content that was downloaded in violation of
the copyright of its respective owners. Please
read the following bulletin and try
solving the problem in one of the recommended ways.
The most vicious problem I-Q Manager or AP Manager (newer version) infection causes is
it may actually lock your computer until you enter a correct
license number for the program.
Thankfully, security researchers found working registration code: RFHM2-TPX47-YD6RT-H4KDM.
Please note that this code is not a solution for this problem and your computer is still infected
with malware. It
only makes the removal procedure easier. In order to completely remove
Copyright violation alert infection please use an
automatic removal tool below. The home page of
this scam is icpp-online.com. You should avoid it. And if you have
already paid that fee, then you
should contact your credit card company and dispute the charges.
Copyright
violation alert properties:
• Changes browser settings
• Shows commercial adverts
•
Connects itself to the internet
• Stays resident in background
7:01 am est
2/24/2012
Clean Up Your Hard Drive
02/24/12 - Just because your PC is being sluggish - or possibly even crashing - doesn't
mean you have major
hardware problems. An overloaded or poorly maintained hard drive can
mimic signs of PC failure. Optimizing your drive
is like organizing and cleaning out a closet. It
makes it much easier for you (or in this case your PC) to find things
efficiently. Two basic steps
in this process are drive cleanup and drive defragmentation.
Drive cleanup scans your hard drive for files you don't need , such as Temporary files stored
during browsing or
program installation. Disk deframentation rearranges your data so it occupies
as much contiguous space as possible. Both
operations improve performance - one by freeing
hard drive space and the other by making it faster for the drive to access
files.
Pick Your Weapon
Windows includes two utilities - Disk Cleanup and Disk Defragmentation - that perform these
tasks. Although both
have been tweaked through several versions of the OS (operating systems)
neither tackles drive maintainance in the optimal
fashion offered by third-party tools.
I won't detail Windows' utilities, prefering instead
to focus on a more powerful third party option.
However, if you want to try them, both are accessible from the Programs
(or all programs) option
in the 'Start' menu under 'Accessories and System Tools'. Note that in Windows 7, Disk
Defragmenter
runs automatically by default (unless you disable it).
My weapon
of choice is iolo's Systems Mechanic ($29.95; www.iolo.com). Best Buy uses this
program to fix PC's. I love its flexible approach
(you can create custom cleanup sets and
schedules) and scope (includes backup and drive repair features as well although
I won't cover
them here).
Depending on your needs, System Mechanic
Pro ($49.95; www.iolo.com) might suit you as well
or better. System Mechanic Pro has everything
you need to Fix, Speed Up and Secure your PC
automatically (automating both drive and system maintenance and optimization).
Just Install It
Installing System Mechanic requires you to Download and Start the Installer. Get System
Mechanic and Click 'Start'
Download or visit http://sm.iolo.com to begin downloading the
installer. This takes less than a minute,
and the interface pops up immediately. When asked if
you would like to save the file, Click 'Save', and save the file.
From the main
pop-up window, The sm_dm.exe icon will appear. Double-click on it to begin the
download. "Confirm Run File"...If
asked if you want to allow the program to make changes to this
computer, click 'Yes'. "Finish download".
Save Installer
Allow the download
to finish.
When the Installer has
finished downloading, you will be given to
option to save the installation file to your computer.
If you want to save a copy, choose Yes,
and save it to a convenient
place on your PC. If you do not need a copy, click No.
When you are finished with this step, the Installer will start
automatically.
Save Installer
Activate and Finish Installation
When the Installer starts, follow its step-by-step instructions until you see a windows that asks
for your License
Information. Carefully type the Activation key and your email address into the
License Information window. Click 'OK'.
Continue following the step-by-step instructions to
complete the installation process.
If System Mechanic does not start immediately after activation, double-click the 'System
Mechanic' desktop icon.
Once System Mechanic has obtained and applied all critical updates,
perform a System Analysis by clicking 'Analyze
Now'.
When
the System Analysis is complete, a full list of system problems will be generated. You can
review and automatically repair
any of these problems by using the options on System
Mechanic's dashboard.
The order in which to repair these problems is a chicken-and-egg question. If your hard drive is
very full, cleanup
is faster if you defragment first. Deframentation is speedier is you remove junk
files first.
During ongoing operations System Mechanic lets you automate operations and then adjust them
as needed. You select
the time, day, frequency and order in which options process. While using
System Mechanic, you can look up useful tips,
information, and instructions by accessing the
built-in help system.
Whole Home License
iolo is proud to present the Whole Home License™, a groundbreaking new approach to software
licensing that
allows you to install your favorite iolo products on all of the PCs in your single
family home.
iolo is the first to break the 3-PC restriction to help you fix, speed up, and secure each and every
one of your
household PCs. This policy allows you to install the products on as many PCs as
you own, no matter how many you have
– all for one low price.
Conclusion
With a program such as System Mechanic automated to your liking, you can relax. Your PC
won't suffer from slowdowns
or freezes due to something as easily repaired as a full or
fragmented drive. 
VirusFighter 02/24/12 - VirusFighter is
a new rogue anti-spyware parasite that tries to trick users into downloading it and then makes attempts to scam them
into purchasing its "full" version. Although it gives users a 30-day trial period, tough it attempts to shut
down your system immediately after boot up, after the trial expires. DO NOT trust VirusFighter, and remove
it ASAP if you've been infected. Use one of the automatic removal tools below to eradicate this parasite from your system
immediately. VirusFighter properties: • Shows commercial adverts • Connects
itself to the internet • Stays resident in background
     
3:05 pm est
RegTool
02/24/12 - RegTool is a potentially unwanted Windows registry cleaner and system optimization
tool. It is advertised
as award-winning advanced registry cleaner with more than 40 useful futures
and tools, such as evidence and registry
cleaner, Internet optimizer, junk file remover, smart disk
defrag and many more. RegTool even claims that it has the
ability to increase the speed of your
PC by 70%. However, some of the risks detected by this program is very doubtful.
For example,
it finds many privacy issues where it shouldn't be. The program also suggests to disable certain
updates and recommends to delete Adobe and Java updater startup entries.
RegTool properties:
• Changes browser settings
• Shows commercial adverts
•
Stays resident in background
2/18/2012
Windows XP/Vista/7 Tune Up
02/18/12 - Over time, Windows accumulates so much clutter that cleaning it up evolves from
minor inconvenience
To major task. Most full service IT Repair Shops will charge you about $70
to clean up your system. Let me show you how
to use one of my favorite utilities (CCleaner) free
www.piriform.com To fix up Windows on your home or small office PC.
CCleaner maintains a database of files that are safe to delete and lets you get rid of them with
just
a few Clicks. It is safer to use than a lot of cleanup software I’ve tested, but you must set it
up properly
to ensure You don’t lose anything you’d rather keep.

Installation and Configuration
Download a copy of
the software, and install it, making sure to remove the check from the ‘Add
CCleaner’ From your browser check
box on the fourth screen of the installation wizard if you are
not interested in that Launch the software and click the
‘Options’ tab on the left. Click the
‘Settings’ box and use the checkboxes To select or deselect
any of the self explanatory options
there. In the ‘Secure Deletion’ section. Choose the ‘Secure File
Deletion’ radio button if you want
to make sure that the things CCleaner deletes are not recoverable. This
dramatically slows
down the cleaning process, so only use it if privacy is a priority.
The Cookies section lets you decide if CCleaner should keep any cookies when cleaning.
Cookies are Files
Web sites use to track your browsing habits, but they also store passwords
and do other useful things. When you delete
all your cookies, you’ll also delete all your stored
passwords and login information for Sites you frequent, so
consider moving those sites’ cookies
to the ‘Cookies To Keep’ section or not Removing cookies at all.
Don’t
worry about the ‘Include’ or ‘ Include Settings’ , as they’re for advanced users.
Now We Start Cleaning
Click the ‘Cleaner’ tab. On the Windows” tab select the ‘Internet Explorer’ files you
wish to
delete. Be Aware that if you delete the Cookies and ‘Autocomplete Form History’, you’ll
need to
retype all saved Login info, passwords, and online forms, so you may want to leave those
unchecked. Only
check items In the ‘Windows Explorer’ section if you want to get rid of them for
privacy reasons. We recommend
Checking everything in the ‘Systems’ section except ‘DNS
Cache’. This speeds up Web browsing.
In The ‘Advanced’ section, the only option worth
checking for privacy reason online is ‘Wipe Free Space’,
Which overwrites all empty areas of the
drive with random data,. This takes a long time , so only enable It every so
often.
On the ‘Applications’
tab select options for your other Web browsers as you did for ‘Internet
Explorer’. The other options are
safe to leave selected. Click ‘Analyze’ to see how much space
you’ll save and then Click ‘Run
Cleaner’.
Now, click the ‘Registry’ tab, click ‘Scan For Issues’ , and click ‘Fix Selected Issues’.
This likely
won’t Have any impact on ‘Window’s’ performance , but it can’t hurt. When prompted,
agree to
back up the Registry. After choosing a location, click ‘Fix All Selected Issues’.
Finally, click the ‘Tools’ tab. Click the ‘Uninstall’ box and see if there are any entries in
the
‘Programs To Remove’ section that you no longer need. Click an unwanted program and click
‘Run
Uninstall’. Then click the ‘Startup’ tab, see if there’s anything on the list that you don’t
use,
click it, and click ‘Disable’. This prevents it from running automatically when Windows boots,
preserving
system resources.
If you can, make a donation to these great developers so they can keep up the good work.
And Remember; 'Repeat
these steps every month to keep Windows operating at its highest
level'.
6:57 am est
2/16/2012
Firewall (Software You Should Have)
02/16/12 - The firewalls job is basically to stand guard between your computer (or network) and
the Internet. It
Monitors the information coming and going and blocks access to anything that
shouldn’t be there. To get The most
protection possible, it’s a good idea to have both a hardware
and software firewall.
Software Firewalls
On the software side , if you have decided to employ a security
suite (Kaspersky Internet
Security) that offers protection against multiple Threats in one program, make sure a firewall
is
included. If you choose to use individual protection Programs (Zonealarm), do some research on
the many firewall
programs available. Make sure you get one that you Feel offers sufficient
security with an interface that is easy to
use.
Built in Firewalls
The other option for a software firewall is to simply use the
one built into Microsoft’s operating
system (I Do Not Recommend This). In Windows XP/Vista/7, the firewall is on
by default, but
you can verify that it hasn’t been turned off Or change its settings by clicking Control Panel
from
the Start menu and then double-clicking Windows Firewall.
It’s important to note that the built-in firewall
in Windows , while a basic layer of protection, is not
Designed to be your PC’s only defense. For example, it can
protect against malicious software
worms But is not designed to guard against viruses or spyware. And if you decide to
use a
separate software Firewall, either as part of a security suite or as standalone software,
remember to turn
off the built-in Windows firewall to avoid any potential conflicts.
Hardware Firewalls
You can also buy standalone hardware firewalls, but many manufacturers
bundle them with
broadband Routers and modems, which are the devices you use to connect to the Internet and
other
types of Networks. If you have a cable or DSL modem or a network router (some devices
function as both Router and modem),
you’ll want to check to see if one or both also have a
firewall built in. Check The manufacturer’s Web site,
users manual, or other documentation to
learn the details of your product And determine how best to set it up to meet
your specific
security needs.
Below, users
can Try (Sample) some of the best Security Suites available.
     
2/14/2012
Common Sense Defense
02/14/12 - Of course, even the most powerful , up-to-date
security suite and network hardware
can’t protect Consumers
from their own bad decisions. There are many scams online that prey
on susceptible Users eager to make a fast buck or get a great product for nothing. These types
of tricky tactics Are nearly impossible to protect against with security software or hardware.
They require a Healthy dose of skepticism and common sense on the
part of the consumer.
Here, a few reminders that sometimes your
brain is your most important security tools:
- If it sounds too good to
be true , it probably is
- Don’t click the link for a program if your security software is telling you not to install it
- Stick
to well known, big brand names with a good reputation
- Know what software you have on your PC and that it’s current
- Remember
to update and scan for viruses daily
- Read end-user license agreements and terms and conditions carefully
- Control
physical access to your systems (most crackers can gain access to password
- Protected systems and even overcome encryption
once they have physical access.
- Your as safe as your latest update
9:51 pm est
DGTFX Virus
02/14/12 - This is an example of the DGTFX Virus Phishing scam that is operating right now.
This
is a scam and if you send the information to these criminals that they are asking for You
Can Kiss Your E-Mail Account GOODBYE!
Legitimate
companies will never ask you to verify or provide confidential or financial
information
in an unsolicited email.
"LAST WARNING*****Tuesday, February 14, 2012 6:37 AM To: undisclosed-recipients
Virus Notification
A DGTFX Virus has been detected in your
Yahoo.com folders. Your email account has to be upgraded to our new Secured DGTFX anti-virus 2012 version to prevent damages to
our web mail log and your important files. Click your reply tab, Fill the columns below and get back to us with
your full account information and get back to us or your email account will be terminated to avoid spread of the virus. Email:
User name:
Password:
Reconfirm Password:
Director of Yahoo.com Technical Team. Note that your password will be encrypted with 1024-bit RSA keys for your password safety.
Thank
you for your co-operation. Warning Code
:ID67565434
4:56 pm est
2/12/2012
Kaspersky Security Suite (Security You Really Need)
02/12/12 - For all the security information out there, it can still be difficult to get a clear
understanding
of exactly what You need to be protected. Many users know they need security
but they have common concerns trying To
understand the protection level and combination that
will allow them to enjoy some peace of mind The next time they are
at their Computer.
Multiple Security Apps
The installation of multiple anti-spyware apps won’t
cause trouble with PCs but the same can not
be said for doubling up on most other security programs, such as antivirus
and firewall programs.
Adding more than one (antivirus or firewall) program to do the same task is probably going to
cause problems on your PC rather than solve them.
Anti-Virus Characteristics
Antivirus programs, even though they may be from different
manufacturers, are designed to
function in Similar ways. They require roughly the same amount of memory and access roughly
the same parts of Your computer to accomplish similar tasks. If you have two antivirus programs
running at the same
time Your computer will become bogged down and sluggish as the RAM
and CPU are unnecessarily taxed twice as hard.
Firewall Characteristics
In the case of Firewalls, trying to run two software firewalls on your computer at once may lead to
more Problems
than just slow performance. Because firewalls control the traffic coming and
going from your Computer by opening and
closing the appropriate ports (points of entry), having
multiple of such Programs running at once could cause problems
with your Internet connectivity
or printing capability.
Limitations
As a professional, I can tell you there are many free programs
available to provide home users
with limited Protection on their personal systems. You can get antispyware, antimalware,
antivirus, firewalls, etc. from Various manufacturers under varying conditions. Some of these
come in the form of Free
Trials and others Allow the user Free Access with a basic protection
package.
Recommendation
The Best suggestion I have for users is investing in Security
Suite software rather than making an
attempt At doubling up your protection programs. A comprehensive Security Suite
(like
Kaspersky) combines protection against malware (spam, viruses, spyware,) worms and more
while also offering a firewall and backup
capabilities. This all-in-one approach cuts down on any
possible overlap that might bog down your computer or gaps in
protection that could leave you
vulnerable.
2/9/2012
Koobface Worm
02/09/12 - Koobface worm is distributed on social networks, usually on MySpace and Facebook.
It embeds itself on
victim’s profile and displays links to malicious websites. The websites
promote video codec which is actually the
Koobface worm. Those sources might also install the
worm without notifying visitors.
Koobface is also known
as W32/Koobface, W32/Koobface.AZ, W32.Koobface and Boface. Once
it gets on a machine, it checks if there are cookies
of social networks. If it finds the cookies, it
infects victim’s profile. If Koobface worm can’t find evidence
of social networking websites, it
simply erases itself.
Koobface also loads pop-ups that look like MS Windows
error messages. The pop-up contains
the following text: “Error installing Codec. Please contact support.”
Use one of the automatic
removal tools listed below to eradicate this parasite.
Koobface properties:
• Connects itself to the internet
• Hides from the user
• Stays resident in background
     
10:17 pm est
Alexa Toolbar
02/09/12 - Alexa Toolbar is a legitimate Internet Explorer plugin that displays helpful information
about visited
web sites, shows relevant links, provides a pop-up blocker and web search service.
The program collects some general
information about the user's web browser and operating
system, records addresses of visited web sites and logs computer
Internet addresses.
Nevertheless, Alexa Toolbar doesn't provide gathered data to third parties and uses it mostly for
demographics and statistics. Alexa Toolbar IS NOT classified as adware or spyware of any kind.
Alexa
Toolbar properties:
• Connects itself to the internet
• Stays resident in background
10:13 pm est
2/5/2012
ALOT Toolbar
12:20 pm est
Internal Conflict Alert 02/05/12
- "Internal Conflict Alert" Pop up is a fallacious security alert form fake spyware remover
called ANG Antivirus
09. The "Internal Conflict Alert" Pop up text is written
below:
"Internal conflict alert!
ANG AntiVirus has detected internal software conflict. Some application
endeavours to access
your system kernel. It may cause irreversible damage to your computer.
Yes, activate ANG AntiVirus
09
No, continue unsecured"
Simply closing the "Internal Conflict Alert" pop-up window won't
help you to get rid of it. In order
to get rid of this officious and fake alert you have to remove ANG Antivirus 09,
because this
rogue produces the "Internal Conflict Alert" pop-up window.
"Internal Conflict Alert" Pop up properties:
• Shows commercial adverts
•
Connects itself to the internet
• Stays resident in background
     
11:58 am est
|
|
Q. How do I avoid rogue antispyware and antivirus software?
A. Make sure you 'Choose Industry Certified "Security Program"
Solutions'!
If your PC is connected to
the internet, uses e-mail, has software of an unknown
origin
installed and comes into contact with recordable media (jump drives, dvd's,
cd's, etc) Antispyware and Antivirus protection is a requirement. They help prevent
attacks through e-mail (and/or attachments sent with e-mail) and surfing the web.
They also help you eradicate infections which are the result
of security holes and
bugs in software. (The e-mail, web surfing
and software holes and bugs result in
the most serious internet
attacks).
One
way to know you're purchasing a trustworthy application is to confirm that
the program
you choose has earned certification from the leading labs.
Industry certification
from ICSA Labs, Virus Bulletin, West Coast Labs, the National
Association
of Specialist Computer Retailers, and others all require antispyware/
antivirus programs to meet stringent requirements to receive certification.
Smartphone and Tablet Tips to create a safe passcode.
Smartphones and tablets open the
door to your Work, friends, family, bank details, etc... No matter which device you use, follow these tips to keep your data secure.
1. Always use a passcode. If someone gets hold of your device, the person has immediate access to your apps and
data.
2. Make your passcode difficult to guess. Codes such as 1234 or 2580 can be cracked in seconds. Go for something that’s
unique but easy for you to remember.
3. Longer is stronger. The longer the passcode, the harder it is to crack. Make yours a minimum of six
digits.
4. Mix numbers and letters. If your device allows, use a passcode that combines numbers, letters and punctuation. Avoid dictionary words and
choose a memorable combination.
5. Make it unique. Don’t use the same passcode for anything else, including other devices,
bank cards or online accounts. That way, if one passcode gets hacked the rest stay secure.
6. Be discreet. Look around and make sure no one is watching you enter your passcode, just as
you would protect your PIN at the ATM machine.
Q. What steps need to be taken to secure
mobile devices (smartphones) for
personal/work phones and
tablets.
A. Follow these steps to secure your mobile
devices.
1. Secure your device
a.
Always lock it
b. Apply a complex passcode
c. Shield your passcode
d. Apply the latest patches
2.
Prevent Malware Infections
a.
Don't click on unsolicited links
b. Think before downloading apps
c. Don't "jailbreak" or "root" your mobile
3.
Be data aware
a.
Be careful what you share
b. Encrypt sensitive data
4. Stay compliant
a. Know and follow your organizations
security
policies
Q. Do you have an example of an Organizational 'Mobile Device Security Policy'
A. Here is EZMobilePC's policy.
1.
Introduction
Mobile devices, such as smartphones and tablet computers, are important tools for the
organization and their use
is supported to achieve business goals.
However, mobile devices
also represent a significant risk to information security and
data security as, if the
appropriate security applications and procedures are not applied,
they can be a conduit for
unauthorized access to the organization’s data and IT
infrastructure.
This can subsequently lead to data leakage and system infection.
EZMoblePC has a requirement to protect its information assets in order to safeguard
its customers, intellectual property and reputation. This document outlines a set of
practices and requirements for the safe use of mobile devices.
2.
Scope
1. All mobile devices, whether owned by EZMoblePC or owned by employees, that have
access to corporate networks, data and systems, not including corporate IT-managed
laptops. This includes smartphones and
tablet computers.
2. Exemptions: Where there is a business need to be exempted from this
policy
(too costly, too complex, adversely impacting other business requirements) a risk
assessment
must be conducted being authorized by security management.
3. Policy - Technical Requirements
1.
Devices must use the following Operating Systems: Android 2.2 or later,
iOS 4.x or later.
2. Devices must store all user-saved passwords in an encrypted password store.
3. Devices must be configured with a secure password that complies with EZMoblePC's
password policy. This password must not be the same as any other credentials used
within the organization.
4.
With the exception of those devices managed by IT, devices are not allowed to be
connected directly to the internal corporate network.
3.1 User Requirements
1.
Users must only load data essential to their role onto
their mobile device(s).
2.
Users must report all lost or stolen devices to EZMoblePC
IT immediately.
3.
If a user suspects that unauthorized access to company
data has taken place
via a mobile device, they must report the incident in alignment
with EZMoblePC’s
incident handling process.
4. Devices must not be “jailbroken”* or have any software/firmware installed
which
is designed to gain access to functionality not intended to be
exposed to the user.
5.
Users must not load pirated software or illegal content
onto their devices.
6.
Applications must only be installed from official platform-owner
approved sources.
Installation of code from un-trusted sources is forbidden.
If you are unsure if an
application is from an approved source contact EZMoblePC IT.
7. Devices must be kept up to date with manufacturer or network provided patches.
As a minimum patches should be checked for weekly
and applied at least once a month.
8.
Devices must not be connected to a PC which does not
have up to date and enabled
anti-malware protection and which does not comply with corporate
policy.
9.
Devices must be encrypted in line with EZMoblePC’s
compliance standards.
10.
Users may must be cautious about the merging of personal
and work email accounts on
their devices. They must take particular care
to ensure that company data is only sent
through the corporate email
system. If a user suspects that company data has been sent
from a personal email account, either in body text or as an attachment, they must notify
EZMoblePC IT immediately.
11.
(If applicable to your organization) Users must not
use corporate workstations to backup
or synchronize device content such as media files, unless such content is required
for
legitimate business purposes.
*To jailbreak a mobile device is to remove the limitations imposed by the manufacturer.
This gives access to the operating system, thereby unlocking all its features and enabling
the installation of unauthorized software.
Q. What is the first thing I should
do when I turn on my computer.
A. Back up important files
If you follow these tips, you're more likely to be free of interference from
hackers,
viruses,
and spammers. But no system is completely secure. If you have important
files stored on your computer, copy them onto a removable disc or
an external
hard
drive, and store it in a safe place.

Q. How do I protect my password?
A. Protect your passwords
Keep your passwords in a secure place, and out of plain sight. Don't share them
on the Internet, over email, or on the phone. Your Internet Service Provider (ISP)
should never ask for your password. In addition, hackers
may try to figure out your
passwords to gain access to your computer. To make it tougher for
them:
Use passwords that have at least eight characters and include numbers or symbols.
The longer the password,
the tougher it is to crack. A 12-character password is
stronger than one with eight characters.
Avoid common word: some hackers
use programs that can try every word in the
dictionary.
Don't use your personal information, your login name, or adjacent keys on the
keyboard as passwords.
Change your passwords regularly (at a minimum, every 90 days).
Don't use the same password for each online account you access.
Q. What steps need to be taken when
setting up Wireless Home Network Security.
1) Change Default Administrator Passwords (and Usernames)
Changing the default password is important because everyone
that purchases the same
Wireless access device, knows your password.
2) Turn on (Compatible) WPA / WEP Encryption
By default, your Wireless device comes
without the encryption enables. WPA / WEP are
security programs that forced your computer to provide
an encrypted password before
you are allowed access
to the wireless access point.
3) Change the Default SSID
SSID is the network name of your wireless network;
most people leave the default name,
such as, Linksys or NetGear. By changing the name, intruders have a more difficult time
identifying your system and use known vulnerabilities. (And
of course, use the unchanged
default password.) One
mistake people make is naming their home network their family
name and or address. When cruising a neighborhood of wireless devices, its always
scary to see Bobsnet444.
4) Disable SSID Broadcast
In Wi-Fi networking, the access point or router typically broadcasts
the network name
(SSID) over the air at
regular intervals. This feature was designed for businesses and
mobile hotspots where Wi-Fi clients may come and go. In the home, this feature is
unnecessary, and
it increases the likelihood an unwelcome neighbor or hacker will try
to
log in to your home network.
5) Assign Static IP Addresses to Devices
Most home networkers gravitate toward using dynamic IP addresses.
This means that
the IP Address, (the IP
Address is needed to participate on a network.) is typically
assigned automatically. A dynamic IP address on an unsecure system can also supply
a hacker with a IP Address.
6) Enable MAC Address Filtering
Each piece of Wi-Fi gear possesses a unique identifier called the "physical address"
or "MAC address." Access points and routers keep
track of the MAC addresses of all
devices that connect to them. Many such products offer the owner an option to key in the
MAC addresses of
their home equipment that restricts the network to only allow
connections from those devices. Do this, but also know that the feature is not so powerful
as it may seem. Hacker software programs
can fake MAC addresses easily.
7) Turn Off the Network During Extended Periods of Non-Use
The ultimate in security measures for any wireless network
is to shut down, or turn office
your wireless access point
when you are not using. You are the most vulnerable at work
or asleep, and mischief minded people know it.
8) Position the Router or Access Point Safely
Wi-Fi signals normally reach to the exterior of a home. A small amount
of "leakage"
outdoors is not a problem,
but the further this signal reaches, the easier it is for others
to detect and exploit. Wi-Fi signals often reach across streets and through neighboring
homes. When installing a wireless home network, the position
of the access point or
router determines it's reach. Try to position these devices near the center of the home
rather than near windows to minimize
this leakage.
Q: What are the first security steps I should take before I connect my computer to the internet?
A: Practices Before You Connect a New Computer to the Internet
We advise home users to download and install software patches
as soon as possible after connecting a
new computer to the
Internet. However, since the background intruder scanning activity
is constant, it may not be possible for the user to complete the
download and installation of software
patches before the vulner-
abilities they are trying to fix are exploited. We recommend the
following actions 'before' connecting computers to the Internet
so
that
users can complete the patching process without incident.
Q. Where do I report
Hacking or Malware activity?
A. Here is where to report:
Hacking or a Computer Virus
Alert the appropriate authorities by contacting: Your ISP and the hacker's ISP (if you can tell what it is). You can
usually find an ISP's email
address on its website. Include information on the
incident from your firewall's log file. By alerting the ISP to the
problem on its system,
you can help it prevent similar problems in the future. The FBI at www.ic3.gov. To
fight computer criminals, they need to hear from you.
Internet
Fraud If a scammer takes advantage of you through an
Internet auction,
when you're shopping
online, or in any other way, report it to the Federal Trade
Commission, at ftc.gov. The FTC enters Internet, identity theft, and other fraud-related complaints into Consumer Sentinel, a secure, online database available to hundreds
of civil and criminal law enforcement agencies in the U.S. and abroad.
Deceptive
Spam If you get deceptive spam, including email phishing
for your
information, forward it
to spam@uce.gov. Be sure to include the full header of the email, including all routing information. You also may report phishing email to
of ISPs, security vendors, financial institutions and law enforcement agencies,
uses these reports to fight phishing.
Divulged
Personal Information If you believe you have mistakenly
given your
personal information to
a fraudster, file a complaint at ftc.gov, and then visit the Federal Trade
Commission's Identity Theft website at ftc.gov/idtheft to learn how to minimize your risk
of damage from a potential theft of your identity.
Parents Parents sometimes can feel outpaced by their technologically savvy
kids. Technology aside, there are lessons that parents can teach to help kids
stay safer as they socialize online. Most ISPs provide parental
controls, or you
can buy separate
software. But no software can substitute for parental supervision.
Talk to your kids about safe computing practices, as well as the things they're
seeing and doing online.
Social Networking
Sites Many adults, teens, and tweens use social networking
sites to exchange information about themselves, share pictures and
videos, and
use blogs and private
messaging to communicate with friends, others who share
interests, and sometimes even the world-at-large. Here are some tips for parents
who want their kids to use these sites safely:
Use privacy settings to restrict who can access and post on your
child's website. Some social networking sites have strong privacy
settings. Show
your child how to
use these settings to limit who can view their online profile, and
explain to them why this is important.
Encourage your child to think about the language used in a blog,
and to think before posting pictures and videos. Employers, college
admissions
officers, team coaches,
and teachers may view your child's postings. Even a kid's
screen name could make a difference. Encourage teens to think about the
impression that screen names could make.
Remind your kids that once they post information online, they can't
take it back. Even if they delete the information from a site, older
versions may
exist on other people's
computers and be circulated online.
Talk to your kids about bullying. Online bullying can take many forms,
from spreading rumors online and posting or forwarding private messages
without
the sender's OK, to sending
threatening messages. Tell your kids that the words
they type and the images they post can have real-world consequences. They can
make the target of the bullying feel bad, make the sender look bad
— and, some-
times, can bring
on punishment from the authorities. Encourage your kids to talk to
you if they feel targeted by a bully.
Talk to your kids about avoiding sex talk online. Recent research
shows that teens who don't talk about sex with strangers online
are less likely to
come in contact
with a predator.
Tell your kids to trust their instincts if they have suspicions. If they feel threatened by
someone or uncomfortable because of something online, encourage
them to tell you.
You can then help
them report concerns to the police and to the social networking
site. Most sites have links where users can immediately report abusive, suspicious,
or inappropriate activity.

Q. What is the best way to keep malware
out.
A.
Try to minimize the threat.
Minimizing
the Effects of Malware on Your Computer
Malware is short for “malicious software;” it includes viruses —
programs that copy
themselves without your permission — and spyware, programs installed without
your consent to monitor or control your
computer activity. Criminals are hard at work
thinking up creative ways to get malware on your computer. They create appealing
web sites, desirable downloads, and compelling
stories to lure you to links that will
download malware, especially on computers that don’t use adequate security
software. Then, they use the malware to
steal personal information, send spam,
and commit fraud.It doesn’t have to be that way.
So says a website with tips from
the federal government and the technology industry that is helping consumers be on
guard against Internet fraud, secure their
computers, and protect their personal
malware can wreak, and reclaim their computers and their electronic information.
Computers may be infected with malware if they:
-
slow down, malfunction, or display repeated error messages;
- wont shut down or restart;
-
serve up a lot of pop-up ads, or display them when youre not surfing
the web;
or
-
display web pages or programs you didnt intend to use, or send emails
you
didnt write.
If you suspect malware
is on your computer
If you suspect malware is lurking on your computer, stop shopping, banking, and
other online activities that involve user names, passwords, or other
sensitive inform-
ation.
Malware on your computer could be sending your personal information to
identity thieves.
Then, confirm that your security software is active and current:
at a minimum, your
computer
should have anti-virus and anti-spyware software, and a firewall. You can
buy stand-alone programs for each element or a security suite that
includes these
programs
from a variety of sources, including commercial vendors or from your
Internet Service Provider. Security software that comes pre-installed on a computer
generally works
for a short time unless you pay a subscription fee to keep it in effect.
In any case, security software protects against the newest threats
only if it is up-to-
date.
Thats why it is critical to set your security software and operating system (like
Windows or Apples OS) to update automatically.
Some scam artists distribute malware disguised as anti-spyware software. Resist
buying software in response to unexpected pop-up messages or emails,
especially
ads
that claim to have scanned your computer and detected malware. Thats a tactic
scammers have used to spread malware, and that has attracted the attention
of the
Federal
Trade Commission, the nations consumer protection agency, as well as a
security tools from legitimate security vendors selected by GetNetWise, a project
of
the Internet
Education Foundation.
Once you confirm that
your security software is up-to-date, run it to scan your compu-
ter for viruses and spyware. Delete everything the program identifies as a problem.
You
may have to restart your computer for the changes to take effect.If you suspect
that your computer still is infected, you may want to run a second anti-spyware
or
anti-virus
program. Some computer security experts recommend installing one
program for real-time protection, and another for periodic scans of your machine
as
a
way to stop malware that might have slipped past the first program.
Finally, if the problem persists after you exhaust your own ability to diagnose and
treat it, you might want to call for professional
help. If your computer is covered by a
warranty that offers free tech support, contact the manufacturer. Before you call,
write down the model and serial number of
your computer, the name of any software
you’ve installed, and a short description of the problem. Your notes will help you give
an accurate description to the technician.If you need professional help, if your
machine isn’t covered by a warranty, or if your security software isn’t
doing the job
properly, you may need to pay for technical support. Many companies — including
some affiliated with retail stores —
offer tech support via the phone, online, at their
store, or in your home. Telephone or online help generally are the least expensive
ways
to access support services — especially if there’s a toll-free helpline — but you
may have to do some of the work yourself.
Taking your computer to a store usually is
less expensive than hiring a technician or repair person to come into your home.
Once your computer is back
up and running, think about how malware could have
been downloaded to your machine, and what you could do to avoid it in the future. If
your security software or operating system was
out-of-date, download the newest
version and set it to update automatically. Use the opportunity to back up important
files by copying them onto a removable disc. Other
ways to minimize the chances
of a malware download in the future:
-
Don’t click on a link in an email or open an attachment unless you
know who sent it and what it is. Links in email can send you to sites
that automatically download malware to your machine. Opening
attachments — even those that appear to come from a friend or
co-worker — also can install malware on your computer.
-
Download and install software only from websites you know and trust.
Downloading free games, file-sharing programs, and customized
toolbars may sound appealing, but free software can come with
malware.
-
Talk about safe computing. Tell your kids that some online activity
can
put a computer at risk: clicking on pop-ups, downloading free games or
programs, or posting personal information.
Finally, monitor your computer
for unusual behavior. If you suspect your machine
has been exposed to malware, take action immediately. Report problems with
malware to your ISP so it can try to prevent similar problems and
alert other

Q. What Should Parents know about Social
Networking Sites?
A. Social Networking
Sites
"It's 10 p.m. Do you know where your
children are?
"Remember that phrase from your own childhood? It's still a valid question, but now, it comes with a twist:
"Do you know where your kids are — and who they're chatting with online?
"Social networking sites have morphed into
a mainstream medium for teens and adults. These sites
encourage and enable people to exchange information
about themselves, share pictures and videos,
and
use blogs and private messaging to communicate with friends,
others who share interests, and
sometimes
even the world-at-large. And that's why it's important
to be aware of the possible pitfalls that
come
with networking online.
Some social networking
sites attract pre-teens – even kids as young as 5 or 6. These younger-focused
sites don't allow the same kinds of communication
that teens and adults have, but there are still things
that parents can do to help young kids socialize
safely online. In fact, when it comes to young kids, the
law provides some protections – and gives parents some control over the type of information that
children can disclose online. For sites directed to children under age 13, and for general audience sites
that know
they're dealing with kids younger than 13, there's the Children's Online Privacy Protection Act
(COPPA). It requires
these sites to get parental consent before they collect, maintain, or use kids'
Information. COPPA also allows parents to review their child's online profiles and blog pages.
Parents sometimes can feel outpaced by their technologically savvy kids.
Technology aside, there are
lessons that parents
can teach to help kids stay safer as they socialize online.
Help Kids Socialize Safely OnlineOnGuard Online shares these tips for safe social networking:
Help
your kids understand what information should be private. Tell them why it's important to
keep some things – about themselves, family members and friends
– to themselves.
Information like their full name, Social Security number, street address, phone number,
and
family financial information — like bank or credit card Account numbers
— is private and
should stay that way. Tell them not to choose a screen name that gives away too
much
personal information.
Use privacy settings to restrict who can access and post on your child's website. Some
social networking sites have strong privacy settings.
Show your child how to use these settings to limit who can view their online profile,
and
explain to them why this is important.
Explain that kids should post only information that you — and they — are comfortable
with others seeing. Even If privacy settings are turned on, some — or even all
— of your
child's profile may be seen by a broader audience Than you're comfortable with.
Encourage your child to think about the language used in a blog, and to think before
Posting pictures and videos. Employers, college admissions officers, team coaches,
and teachers may view your child's postings.
Even a kid's screen name could make a difference. Encourage teens to think about the
impression that screen names could make.
Remind your kids that once they post information online, they can't take it back.
Even if they delete the Information from a site, older versions may exist on other
people's computers and be circulated online.
Know how your kids are getting online. More and more, kids are accessing the Internet
through their cell phones.
Find out about what limits you can place on your child's cell phone. Some cellular
companies have plans that limit downloads, Internet access, and texting; other plans
allow kids to use those features only at certain times of day.
Talk to your kids about bullying. Online bullying can take many forms, from spreading
rumors online and posting or forwarding private messages without the sender's
OK, to
sending threatening messages. Tell your kids that the words they type and the
images
they post can have real-world consequences. They can make the target of the
bullying feel bad, make the sender look bad – and, sometimes, can bring on
punishment from the authorities.
Encourage your kids to talk to you if they feel targeted by a bully.
Talk to your kids about avoiding sex talk online. Recent research shows that teens who
don't talk about sex with strangers online are less likely to come in contact with
a
predator.If you're concerned that your child is engaging in risky online behavior,
you can
search the blog sites they visit to see whatinformation they're posting. Try searching
by their name, nickname, school, hobbies, grade, or area where you live.
Tell your kids to trust their gut if they have suspicions. If they feel threatened by someone
or uncomfortable because of something online, encourage them to tell you. You
can then
help them report concerns to the police and to the social networking site. Most
sites have
links where users can immediately report abusive, suspicious, or inappropriate
online
behavior.
Read sites'
privacy policies. Spend some time with a site's privacy policy, FAQs, and
parent sections to Understand its features and privacy controls. The site should
spell out
your rights as a parent to review and delete your child's profile if your child
is younger
than 13.
A Few More Tips to Protect Pre-TeensMany of the tips above apply for pre-teens, but
parents of younger children also can:
Take
extra steps to protect younger kids. Keep the computer in an open area like the
kitchen or family room, so you can keep an eye on what your kids are doing online.
Use the Internet with them to help develop safe surfing habits.
Consider taking advantage of parental control features on some operating systems
that let you manage your kids' computer use, including what sites they can visit,
whether they can download items, or what time of day they can be online.
Go where your kids go online. Sign up for – and use – the social networking spaces
that your kids visit. Let them know that you're there, and help teach them how to act
as they socialize online.
Review your child's friends list. You may want to limit your child's online “friends” to
people your child actually knows and is friendly with in real life.
Understand sites' privacy policies. Sites should spell out your rights as a parent to
review and delete your child's profile if your child is younger than 13.
For More InformationTo learn more about staying safe online, visit the websites of the following organizations:
Federal Trade Commission — www.OnGuardOnline.gov The FTC works for the consumer to prevent fraudulent, deceptive, and unfair business
practices in the marketplace and toprovide information to help consumers spot, stop, and avoid them.
To file a complaint or to get free information onconsumer issues, visit ftc.gov or call toll-free, 1-877-FTC-HELP
(1-877-382-4357); TTY: 1-866-653-4261.The FTC manages OnGuardOnline.gov, which provides practical tips
from the federal government and the technologyindustry to help you be on guard against Internet fraud,
secure your computer, and protect your personal information. ConnectSafely — www.connectsafely.org ConnectSafely is a forum for parents, teens, educators, and advocates designed
to give teens and parents a voice in thepublic discussion about youth online safety, and has tips, as
well as other resources, for safe blogging and socialnetworking. Along with NetFamilyNews.org, it is
a project of the non- profit Tech Parenting Group. Cyberbully411 — www.cyberbully411.org Cyberbully411 provides resources and opportunities for discussion and sharing
for youth - and their parents - who havequestions about or may have been targeted by online harassment.
The website was created by the non-profit Internet Solutions for Kids, Inc., with funding from the Community
Technology Foundation of California. GetNetWise — www.getnetwise.org GetNetWise is a public service sponsored by Internet industry corporations and
public interest organizations to helpensure that Internet users have safe, constructive, and educational
or entertaining online experiences. The GetNetWise coalition works to provide Internet users with the
resources they need to make informed decisions about their and theirfamily's use of the Internet.
iKeepSafe.org is a coalition of 49 governors/first spouses, law enforcement,
the American Medical Association, the American Academy of Pediatrics, and other associations dedicated
to helping parents, educators, and caregivers byproviding tools and guidelines to promote safe Internet
and technology use among children.
NCMEC is a private, non-profit organization that helps prevent child abduction
and sexual exploitation; helps find missingchildren; and assists victims of child abduction and sexual
exploitation, their families, and the professionals who serve them. staysafe —
www.staysafe.org staysafe.org is an educational site intended to help
consumers understand both the positive aspects of the Internet aswell as how to manage a variety of
safety and security issues that exist online.
WiredSafety.org is an Internet safety and help group. WiredSafety.org provides
education, assistance, and awareness on cybercrime and abuse, privacy, security, and responsible technology
use. It is also the parent group of Teenangels.org, FBI-trained teens and preteens who promote Internet
safety. See also: Social Networking Sites: Safety Tips for Tweens and Teens What to Do if There's a ProblemTrust your gut if you have
suspicions. If you feel threatened by someone or uncomfortable because of something online,Tell an adult
you trust, and report it to the police and the social networking site.The Children's Online Privacy
Protection Act (COPPA) requires websites to obtain parental consent before collecting, using,or disclosing
personal information from children under age 13.
Q. What are
Nigerian con-men or internet scams?
A.
Phony Lotteries, Nigerian 419s, Advanced Fee Fraud, and Scams
While you're online:
Know who you're
dealing with.
In any electronic transaction, independently confirm the other party's name, street
address, and telephone number.
Resist the urge to enter foreign lotteries. These solicitations are phony
and illegal.
Delete requests that claim to be from foreign nationals
asking you to help transfer their money through your bank account. They're fraudulent.
Ignore unsolicited
emails that request your money, credit card or account numbers, or other personal information.
If you are selling something over the Internet, don't accept a potential buyer's offer to send you a check
for more than the purchase price, no matter how tempting the plea or convincing the story. End the transaction immediately
if someone insists that you wire back funds.The Internet gives buyers access to a world of goods and services, and gives sellers access to a world of customers.
Unfortunately, the Internet also gives con artists the very same access. But being on guard online can help you maximize the
global benefits of electronic commerce and minimize your chance of being defrauded. OnGuard Online wants you to know how to
spot some cross-border scams — including foreign lotteries, money offers, and check overpayment schemes — and
report them to the appropriate authorities.
Foreign Lotteries
For years, scam operators have used the telephone and direct mail to entice U.S. consumers into buying chances in supposedly
high-stakes foreign lotteries. Now they're using email, too — either to sell tickets or suggest that a large cash prize
has your name on it. No matter what country's name is used to promote a lottery, the pitch follows a pattern: you should send
money to pay for taxes, insurance, or processing or customs fees. The amount may seem small at first, but as long as you keep
paying, the requests for funds will keep coming — for higher and higher amounts. Some victims have lost thousands of
dollars.Most scam operators never buy the lottery tickets on your behalf. Others buy some tickets, but keep the "winnings"
for themselves. In any case, lottery hustlers generally try to get you to share your bank account or credit card numbers,
so they can make unauthorized withdrawals.If you're thinking about responding to a foreign lottery, OnGuard Online wants you to remember:
Playing
a foreign lottery is against the law.
There are no secret systems for winning foreign lotteries. Your chances of getting any money back are
slim to none.
If you buy even one foreign lottery ticket, you can expect many more bogus offers
for lottery or investment "opportunities." Your name will be placed on "sucker lists" that fraudsters
buy and sell.
Keep your
credit card and bank account numbers to yourself. Scam artists often ask for them during an unsolicited sales pitch. Once
they get your account numbers, they may use them to commit identity theft.Resist solicitations for foreign lottery promotions. Report them to the appropriate government officials, then hit delete.View a sample fraudulent foreign lottery solicitation.
"Nigerian" Foreign Money Offers
The "Nigerian" scam got its name from emails that supposedly came
from Nigerian "officials" who needed your help getting at their money — which was tied up due to strife in
their country. Today, people claiming to be officials, businesspeople, or the surviving relatives of former government honchos
in countries around the world send countless offers via email to transfer thousands of dollars into your bank account if you
will just pay a fee or "taxes" to help them access their money. If you respond to the initial offer, you may receive
documents that look "official." But then, you will get more email asking you to send more money to cover transaction
and transfer costs, attorney's fees, blank letterhead, and your bank account numbers, among other information. Subsequent
emails will encourage you to travel to another country to complete the transaction. Some fraudsters have even produced trunks
of dyed or stamped money to verify their claims.The emails are from crooks trying to steal your money or commit identity
theft. Victims of this scam report that emergencies arise that require more money and delay the "transfer" of funds;
in the end, you lose your money, and the scam artist vanishes. According to the U.S. State Department, people who have responded
to these solicitations have been beaten, subjected to threats and extortion, and in some cases, murdered.If you receive an
email from someone claiming to need your help getting money out of another country, don't respond. After all, why would a stranger from another country pick you out at random to share thousands of
dollars? Report the solicitation to the appropriate government officials, and then hit delete.View a sample fraudulent foreign money offer.
Check Overpayment Schemes
Say
no to a check for more than your selling price, no matter how tempting the plea or convincing the story. Check overpayment
schemes generally target people who have posted an item for sale online. The con artist, posing as a potential buyer from
a foreign country (or a distant part of the U.S.), emails the seller and offers to buy the item with a cashier's check, money
order, personal check, or corporate check. Or the scammer may pretend to be a business owner from a foreign country, needing
"financial agents" to process payments for their U.S. orders; in exchange, they promise a commission.Regardless of the cover, here's what happens:
The scammer sends you a check that looks authentic — complete with watermarks — made payable for more money than
you expected. They ask you to deposit it in your bank account, and then wire-transfer some portion of the funds to a foreign
account. They provide convincing reasons why the check is for more than the necessary amount, and why the funds must be transferred
quickly. Sometimes, the counterfeit checks fool a bank teller, but be aware that the check still can bounce. The scammer vanishes
with the money you wired from your own account and you are on the hook for the entire amount of the worthless check. In addition,
a scammer who has your bank account number is likely to use it to withdraw more money from your account.
Reporting a Cross-Border Scam
If you think you may have responded to a cross-border scam, file a complaint at www.econsumer.gov, a project of 20 countries of the International Consumer Protection and Enforcement
Network. Then visit the FTC's identity theft website at www.ftc.gov/idtheft. While you can't completely control whether you will become a victim
of identity theft, you can take some steps to minimize your risk.If you've responded to a "Nigerian" scheme, contact your
local Secret Service field office using contact information from the Blue Pages of your telephone directory, or from www.secretservice.gov/field_offices.shtml.In addition, report telemarketing fraud and check overpayment scams to your state
Attorney General, using contact information at www.naag.org.Report unsolicited email offers to spam@uce.gov — including offers inviting you to participate in a foreign
lottery, looking for help getting money out of a foreign country, or asking you to wire back extra funds from a check you
received.If you receive what looks like lottery material from a foreign country through the postal mail, give it to your local
postmaster.
For More InformationForeign Lottery Scams
U.S. Federal Trade Commission — The FTC works for the consumer to prevent fraudulent, deceptive,
and unfair business practices in the marketplace and to provide information to help consumers spot, stop, and avoid them.
To file a complaint or to get free information on consumer issues, visit www.ftc.gov or call toll-free, 1-877-FTC-HELP (1-877-382-4357); TTY: 1-866-653-4261.
The FTC enters Internet, telemarketing, identity theft, and other fraud-related complaints into Consumer Sentinel, a secure,
online database available to hundreds of civil and criminal law enforcement agencies in the U.S. and abroad.Competition Bureau in Canada — The Competition Bureau is an independent law enforcement agency
in Canada that investigates anti-competitive practices and promotes compliance with the
laws under its jurisdiction. To file a complaint or to get free information, visit www.competitionbureau.gc.ca or call toll-free, 1-800-348-5358. The Bureau has the ability to refer criminal matters to the Attorney General of Canada,
who then decides whether to prosecute before the courts.United Kingdom's Office of Fair Trading — The United Kingdom's
Office of Fair Trading is responsible for making markets work well for consumers. They protect and promote consumer interests
throughout the United Kingdom, while ensuring that businesses are fair and competitive. To file a complaint or to get free information,
visit www.oft.gov.uk or send an email to enquiries@oft.gsi.gov.uk.Australian Competition and Consumer Commission — The Australian Competition and Consumer Commission encourages vigorous
competition in the marketplace and enforces consumer protection and fair trading laws. To file a complaint or to get more
information, visit www.accc.gov.au. The ACCC advocates consultation and negotiation as the first and
best option to settle disputes, but once the ACCC pursues legal action any sort of mediation becomes less likely.
"Nigerian" Advance-Fee Scams
U.S. Secret Service — The Secret Service investigates violations of laws relating to financial
crimes, including access device fraud, financial institution fraud, identity theft, and computer fraud. To file a complaint
or to get free information, visit www.secretservice.gov or call 202-406-5708.U.S. Department of State — The Department of State's mission is to create a more secure, democratic,
and prosperous world for the benefit of the American people and the international community. As part of that mission, the
Department of State seeks to minimize the impact of international crime, including cross-border internet scams, on the United States and its citizens. To get free information, visit www.state.gov.
Q. What should I do prior to disposing of an old computer?
A. Computer Disposal
Once you have a “clean” computer,
consider recycling, donating, or reselling it – and keep the environment in mind when
disposing of your computer.If you want to get rid of your old computer, options include recycling,
reselling, and donating.
But before
you log off for thelast time, there are important
things to do to prepare it for disposal. Computers
often hold
personal and financial
information, including passwords, account numbers, license keys or registration numbers for software
programs, addresses and phone numbers, medical and prescription information, tax returns, and other personal documents.
Before getting rid of your old computer, it’s a good idea to use software to “wipe”the hard drive clean. If you don’t, consider
your old hard drive a 21st century treasure chest for identity thieves
and information pirates. The Federal Trade Commission
(FTC), the nation’s consumer
protection agency, says you can deter identity theft and information piracy by taking a few
preventive steps.
Understanding Hard Drives
A computer’s hard
drive stores data, and maintains an index of files. When you save a file, especially a large one, it is
scattered around the hard drive in bits and
pieces. Files also are automatically created by browsers
and operating
systems. When you open a file, the hard drive checks the index, then gathers
the bits and pieces and reconstructs them.
When you
delete a file, the links between the index and the file disappear, signaling to your system that the file isn’t needed
any longer and that hard drive space
can be overwritten. But the bits and pieces of the deleted file stay on your computer
until they’re overwritten, and they can be retrieved with a data recovery program.
To remove data from your hard drive
permanently,
it needs to be wiped clean.
Cleaning Hard Dives
Before you clean your hard
drive, save the files that are important to you on an external storage device – for example,
a USB drive, a CDRom, or an external
hard drive – or transfer them to a new computer. Check your owner’s manual, the
manufacturer’s website, or its customer support line for information on how to
save data and transfer it to a new
computer. Utility programs to wipe your hard drive are available both online and in stores where computers are
sold.
They’re generally inexpensive; some are available on the Internet for free. Wipe utility
programs vary in their capabilities:
some
erase the entire disk, while others allow you
to select files or folders to erase. They also vary in their effectiveness:
programs that overwrite
or wipe the hard drive many times are very effective; those that overwrite or wipe the drive only once
may not prevent information being wiped from being recovered later.
If your old computer contains sensitive information
that would be valuable to an identity
thief, consider using a program that overwrites or wipes the hard drive many times. Or,
remove the hard
drive, and physically destroy it. One more thing to keep in mind: If you use your home or personal
computer
for business purposes, check with your employer about how to manage information on your computer that’s business-related.
The law requires businesses to follow
data security and disposal requirements for certain information that’s related to
customers.
Disposal
Options
Once you have a “clean”
computer, here’s how to dispose of it:
Recycle it. Many computer manufacturers have programs to recycle computers
and components. Check their
websites or call their toll-free numbers
for more information. The Environmental Protection Agency (EPA) has
information on electronic product recycling
programs at
program. Check with your county or local government,
including the local landfill office for regulations.
Donate it. Many organizations collect old computers and donate them to charities.
Resell it. Some people and organizations buy old computers.
Check online. Keep
the environment in mind when disposing of your computer.
Most computer equipment contains hazardous materialsthat don’t belong in a landfill.
For example, many computers have heavy metals that can contaminate the earth.
The EPA recommends that you check with your local health and sanitation agencies for ways to dispose
of electronics safely.
www.hypersmash.com
hostgator promo